Most Common Reasons for Cyber Attacks
The Internet has become a major part of our lives. From shopping to banking, social media to entertainment, the Internet is now a vital part of daily life. As such, it is no surprise that hackers are constantly looking for ways to exploit vulnerabilities in our system in order to gain unfiltered access to sensitive information or steal valuable assets.
Cyber security experts say that cyberattacks are becoming more sophisticated every day. Hackers are using new techniques to break into networks, steal data, and disrupt operations. In addition, they are also targeting organizations’ financial systems, corporate secrets, and customer data. Read more about it on Ethyca Privacy.
Cybercrime

The number of cyberattacks has increased over the years. In 2016 alone, there were 2.5 million reported incidents worldwide. This means that hackers are becoming smarter and more sophisticated at their craft. They are also using new techniques to target individuals and organizations alike.
Cybercrime is growing rapidly due to the increasing dependence on information technology (IT). Hackers are targeting businesses and government agencies because they provide a lucrative opportunity for them. So what exactly causes these attacks? Here are the most common reasons hackers target organizations.
1. Malware

Malware is software used to steal information or disrupt computer systems. Hackers may install malware to spy on users, steal personal information, or shut down computers.
2. Phishing
Phishing involves sending emails that look like they come from legitimate sources but actually contain malicious links or attachments. These emails trick recipients into providing their sensitive information, such as login credentials, or clicking on links that download viruses onto their devices.
3. Ransomware
Ransomware is software that locks files on a user’s device until he pays a ransom. Once the victim pays, the hacker unlocks the files.
4. DDoS Attacks
Distributed Denial of Service (DDoS) attacks involve flooding websites with traffic so they become unavailable to visitors. They also slow down access to email servers and social media platforms.
5. Social Engineering
Social engineering occurs when attackers trick individuals into revealing confidential information. For instance, they may pose as employees of a company and ask for passwords or bank account numbers. Or they may pretend to be calling from a trusted source, such as a government agency, and try to convince victims to give out private details.
6. Business Email Compromise
Business email compromise (BEC) scams involve criminals posing as executives of large corporations and asking for money via wire transfers. Victims think they’re transferring funds to the organization’s bank account, only to find out later that they were tricked.
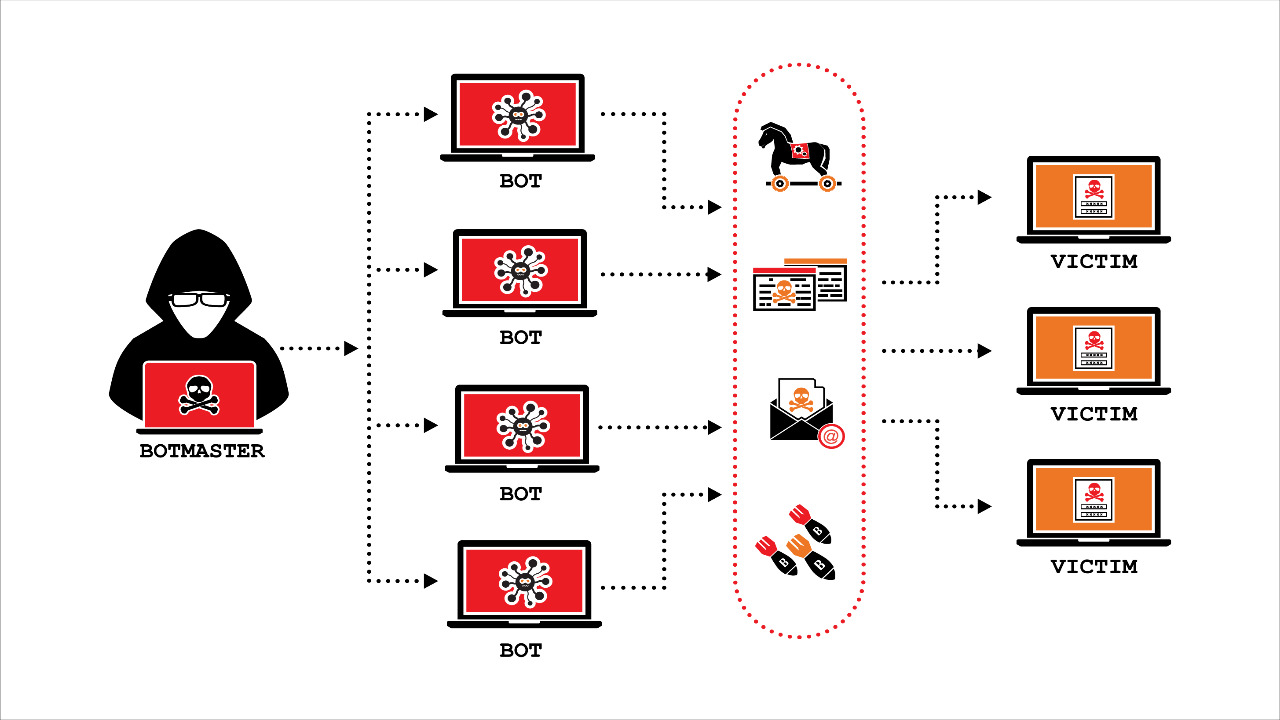
7. Botnets
Botnets are networks of infected computers controlled by hackers. Bots are automated tools that perform tasks automatically without human intervention. Some botnets are used to launch DDoS attacks, while others are used to distribute spam messages.
8. Financial Fraud

Financial fraud is the number one reason hackers attack businesses. Hackers steal money from banks, credit unions, and other financial institutions by stealing information like bank account numbers, PIN codes, and passwords. They also hack into systems to change transaction amounts and make unauthorized purchases.
9. Data Theft
Hackers steal personal information like names, addresses, Social Security numbers, driver’s license numbers, and email addresses. They sell this information to identity thieves who use it to commit crimes like tax evasion, fraudulent insurance claims, and illegal immigration.
10. Intellectual Property Theft
Businesses lose intellectual property when hackers break into their computer networks and steal trade secrets, company plans, product designs, and customer lists. These stolen assets can later be used to compete unfairly against the victim.
11. Identity Theft by hackers
Identity theft by hackers occurs when a hacker uses another person’s personal information to commit crimes. For example, hackers steal social security numbers and open fake bank accounts in the victim’s name. They then transfer funds out of the victim’s account and spend the money themselves.

